MontyB
All-Blacks Supporter
[FONT="]In the course of the war modern cipher machines were designed and built to replace the old systems and securely cover all types of traffic. In 1942 the M-209 device was used in the field and in 1943 the cipher teleprinters Converter M-228 - SIGCUM and SIGTOT were introduced in communications networks. In the summer of ’43 a new speech privacy device called SIGSALY became operational and the first system was used on the link Pentagon-London. In late 1943 the CCM - Combined Cipher Machine was used in the Atlantic and in 1944-45 the British relied on the CCM as much as they did on their own Typex. [/FONT]
[FONT="]By the end of the war the Americans were using several types of cipher machines, all offering a high level of security. William Friedman, head of cipher research at the Army Security Agency, stated in his 1945 reports that the primary US cipher machines SIGABA and Converter M-228 had proven completely secure against enemy cryptanalysts.[/FONT]
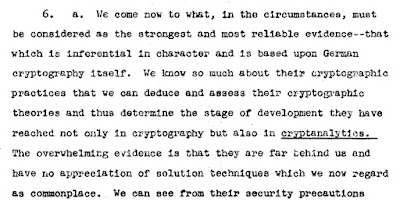
[FONT="]In the report ‘Security of our high-grade cryptographic systems’, dated March 1945 he said:[/FONT]
[FONT="]‘We come now to what, in the circumstances, must be considered as the strongest and most reliable evidence—that which is inferential in and is based upon German cryptography itself. We know so much about their practices that we can deduce and assess their cryptographic theories and thus determine the stage of development they have reached not only in cryptography but also in cryptanalytics. The overwhelming evidence is that they are far behind us and have no appreciation of solution techniques which we now regard as commonplace’.[/FONT]
 [FONT="]‘To summarize: At the risk of sounding boastful, it will be stated that the Japanese are not as good as the Germans, and the latter are not as good as we are in cryptography and especially in cryptanalysis……[/FONT][FONT="]the conclusion must therefore be clear: They cannot read and are not reading our high-grade cipher traffic[/FONT][FONT="]’.[/FONT]
[FONT="]‘To summarize: At the risk of sounding boastful, it will be stated that the Japanese are not as good as the Germans, and the latter are not as good as we are in cryptography and especially in cryptanalysis……[/FONT][FONT="]the conclusion must therefore be clear: They cannot read and are not reading our high-grade cipher traffic[/FONT][FONT="]’.[/FONT]
[FONT="]In the report ‘important contributions to communications security, 1939-1945; summary of contributions made by mr. Friedman’, he said about SIGABA and SIGCUM: [/FONT]
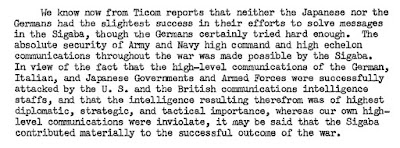
[FONT="]‘We know now from Ticom reports that neither the Japanese nor the Germans had the slightest success in their efforts to solve messages in the Sigaba, though the Germans certainly tried hard enough. The absolute security of Army and Navy high command and high echelon communications throughout the war was made possible by the Sigaba’.[/FONT]
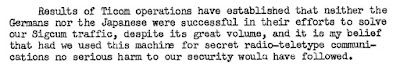
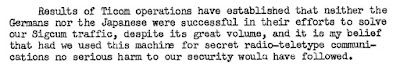
 [FONT="]‘Results of Ticom operations have established that neither the Germans nor the Japanese were successful in their efforts to solve our Sigcum traffic, despite its great volume, and it is my belief that had we used this machine for secret radio-teletype communications no serious harm to our security would have followed’. [/FONT]
[FONT="]‘Results of Ticom operations have established that neither the Germans nor the Japanese were successful in their efforts to solve our Sigcum traffic, despite its great volume, and it is my belief that had we used this machine for secret radio-teletype communications no serious harm to our security would have followed’. [/FONT]
 [FONT="]Was Friedman correct? Were all high grade US cipher machines secure during the war? [/FONT]
[FONT="]Was Friedman correct? Were all high grade US cipher machines secure during the war? [/FONT]
[FONT="]The US cipher teleprinter – information from the war diary of Inspectorate 7/VI [/FONT]
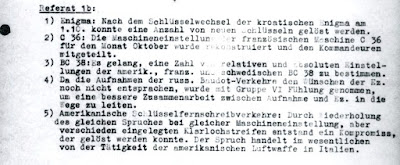
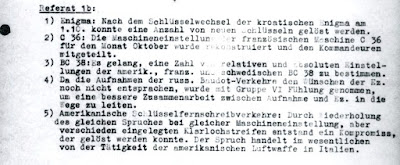
[FONT="]The war diary of the German Army’s signal intelligence service OKH/Inspectorate 7/VI, says that in 1944 they investigated US cipher teleprinter traffic (Baudot FF5). In October ’44 the report of Referat 1b says:[/FONT]
[FONT="]‘Amerikanische schlüsselfernschreibverkehre:[/FONT]
[FONT="]Durch ziederholung des gleichen spruches bei gleicher maschineneinstellung, aber verschieden eingelegten Klarlochstreifen entstand ein Kompromiss, der gelöst werden konnte. Der spruch handelt im wesentlichen von der Tätigkeit der amerikanischen Luftwaffe in Italien[/FONT][FONT="]’.[/FONT]
[FONT="]
[/FONT]
[FONT="]Translation by Frode Weierud:[/FONT]
[FONT="]‘American cipher teleprinter traffic:[/FONT]
[FONT="]By repeating the same message with the same machine settings, but with the clairtext tape placed differently (offset in the tape reader), a compromise occurred that allowed the message to be solved. The message concerned mainly the activity of the American Air Force in Italy[/FONT][FONT="]’.[/FONT]
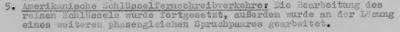
[FONT="]In November-December ’44 they continued to investigate the compromise. In January ’45 the report says that they analyzed the pure key and attempted to solve another pair of messages ‘in phase’:[/FONT]
[FONT="]‘Referat 1b[/FONT]
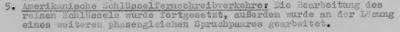
[FONT="]Amerikanische schlüsselfernschreibverkehre:[/FONT]
[FONT="]Die bearbeitung des reinen Schlüssels wurde fortgesetzt, ausserdem wurde an der Lösung eines weiteren phasengleichen Spruchpaares gearbeitet[/FONT][FONT="]’.[/FONT]
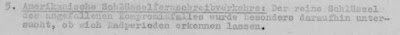
[FONT="]In February ’45 they attempted to find the period of the cipher wheels:[/FONT]
[FONT="]‘Referat 1b[/FONT]
[FONT="]Amerikanische schlüsselfernschreibverkehre:[/FONT]
[FONT="]Der reine Schlüssel des angefallenen kompromissfalles wurde besonders daraufhin untersucht, ob sich Radperioden erkennen lassen[/FONT][FONT="]’.[/FONT]
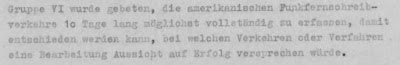
[FONT="]The final report of March ’45 says that 300 5-figure and 300 5-letter messages of US teleprinter traffic (USA-Führungsverkehr Baudot) would be examined by Referat 2a for deciphering opportunities. The actual report of Referat 2a says that Group VI asked for the complete interception of American radio telex traffic for 10 days, in order to decide which cipher procedures would be examined for solution. [/FONT]
[FONT="]‘Referat 2a[/FONT]
[FONT="]Gruppe VI wurde gebeten, die amerikanischen Funkfernschreibverkehre 10 Tage lang möglichst vollständing zu erfassen, damit entschieden werden kann, bei welchen Verkehren oder verfahren eine Bearbeitung Aussicht auf erfolg versprechen würde[/FONT][FONT="]’.[/FONT]
[FONT="]
[/FONT]
[FONT="]Speculation on the ‘Amerikanische schlüsselfernschreibverkehre’[/FONT]
[FONT="]Unfortunately the US cipher teleprinter cannot be identified from the German reports. However the list of possible US cipher machines is short. In 1944 the US Armed Forces used the teleprinters Sigtot and Sigcum plus there is a small chance of the Sigaba being used to send this traffic even though it was not a teleprinter.[/FONT]
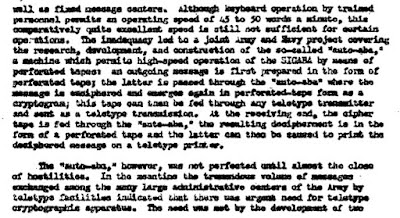
[FONT="]1). SIGABA: The Converter M-134-C/ECM MARK II was an offline cipher machine but the report ‘Achievements of the Signal Security Agency in World War II’, p42 says that it had an ‘auto’ function which printed the ciphertext in a teleprinter tape which could then be sent via a teleprinter unit for rapid transmission. [/FONT]
[FONT="]2). SIGTOT: The sigtot teleprinter was a one time tape system, meaning that each transmission used a tape of randomly generated output in order to ensure that no one could decrypt the contents of the message. If the same tape was used twice then it would be possible to solve that particular message but not additional ones. [/FONT]
3). SIGCUM/SIGHUAD: The Converter M-228 SIGCUM and its modification SIGHUAD were used in large numbers in the period 1943-45. The report ‘important contributions to communications security, 1939-1945; summary of contributions made by mr. Friedman’, p6 says:
[FONT="]‘By 5 June 1944 a total of 3.200 of these machines had been built and 1.488 issued for use, including 200 to the Navy. The machine was employed to encipher a tremendous volume of traffic, including raw material for cryptanalysis from all intercept stations. Under the special conditions and with some modification (Sighuad) the machine was also used in special circuits in Washington, between Arlington Hall Station, the Military Intelligence Service in The Pentagon, of the highest classification. This same modification (Sighuad) permitted the machine to be used by the Air Forces in the U. S. and in the Pacific, to transmit, by radio meteorological and weather data, thus greatly facilitating operations’.[/FONT]
[FONT="]At this time we can only speculate but it seems reasonable to assume that the system the Germans called ‘Amerikanische schlüsselfernschreibverkehre’ was probably the Converter M-228. [/FONT]
The expert on cipher teleprinters at Inspectorate 7/VI was the mathematician Heinrich Döring. It is again reasonable to assume that he was one of the people who examined and solved this traffic.
http://chris-intel-corner.blogspot.hu/2016/01/compromise-of-us-cipher-teleprinter-in.html
[FONT="]By the end of the war the Americans were using several types of cipher machines, all offering a high level of security. William Friedman, head of cipher research at the Army Security Agency, stated in his 1945 reports that the primary US cipher machines SIGABA and Converter M-228 had proven completely secure against enemy cryptanalysts.[/FONT]
[FONT="]In the report ‘Security of our high-grade cryptographic systems’, dated March 1945 he said:[/FONT]
[FONT="]‘We come now to what, in the circumstances, must be considered as the strongest and most reliable evidence—that which is inferential in and is based upon German cryptography itself. We know so much about their practices that we can deduce and assess their cryptographic theories and thus determine the stage of development they have reached not only in cryptography but also in cryptanalytics. The overwhelming evidence is that they are far behind us and have no appreciation of solution techniques which we now regard as commonplace’.[/FONT]
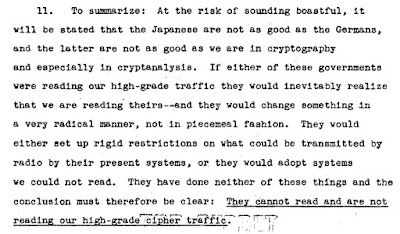
[FONT="]In the report ‘important contributions to communications security, 1939-1945; summary of contributions made by mr. Friedman’, he said about SIGABA and SIGCUM: [/FONT]
[FONT="]‘We know now from Ticom reports that neither the Japanese nor the Germans had the slightest success in their efforts to solve messages in the Sigaba, though the Germans certainly tried hard enough. The absolute security of Army and Navy high command and high echelon communications throughout the war was made possible by the Sigaba’.[/FONT]
[FONT="]The US cipher teleprinter – information from the war diary of Inspectorate 7/VI [/FONT]
[FONT="]The war diary of the German Army’s signal intelligence service OKH/Inspectorate 7/VI, says that in 1944 they investigated US cipher teleprinter traffic (Baudot FF5). In October ’44 the report of Referat 1b says:[/FONT]
[FONT="]‘Amerikanische schlüsselfernschreibverkehre:[/FONT]
[FONT="]Durch ziederholung des gleichen spruches bei gleicher maschineneinstellung, aber verschieden eingelegten Klarlochstreifen entstand ein Kompromiss, der gelöst werden konnte. Der spruch handelt im wesentlichen von der Tätigkeit der amerikanischen Luftwaffe in Italien[/FONT][FONT="]’.[/FONT]
[FONT="]
[/FONT]
[FONT="]Translation by Frode Weierud:[/FONT]
[FONT="]‘American cipher teleprinter traffic:[/FONT]
[FONT="]By repeating the same message with the same machine settings, but with the clairtext tape placed differently (offset in the tape reader), a compromise occurred that allowed the message to be solved. The message concerned mainly the activity of the American Air Force in Italy[/FONT][FONT="]’.[/FONT]
[FONT="]In November-December ’44 they continued to investigate the compromise. In January ’45 the report says that they analyzed the pure key and attempted to solve another pair of messages ‘in phase’:[/FONT]
[FONT="]‘Referat 1b[/FONT]
[FONT="]Amerikanische schlüsselfernschreibverkehre:[/FONT]
[FONT="]Die bearbeitung des reinen Schlüssels wurde fortgesetzt, ausserdem wurde an der Lösung eines weiteren phasengleichen Spruchpaares gearbeitet[/FONT][FONT="]’.[/FONT]
[FONT="]In February ’45 they attempted to find the period of the cipher wheels:[/FONT]
[FONT="]‘Referat 1b[/FONT]
[FONT="]Amerikanische schlüsselfernschreibverkehre:[/FONT]
[FONT="]Der reine Schlüssel des angefallenen kompromissfalles wurde besonders daraufhin untersucht, ob sich Radperioden erkennen lassen[/FONT][FONT="]’.[/FONT]
[FONT="]The final report of March ’45 says that 300 5-figure and 300 5-letter messages of US teleprinter traffic (USA-Führungsverkehr Baudot) would be examined by Referat 2a for deciphering opportunities. The actual report of Referat 2a says that Group VI asked for the complete interception of American radio telex traffic for 10 days, in order to decide which cipher procedures would be examined for solution. [/FONT]
[FONT="]‘Referat 2a[/FONT]
[FONT="]Gruppe VI wurde gebeten, die amerikanischen Funkfernschreibverkehre 10 Tage lang möglichst vollständing zu erfassen, damit entschieden werden kann, bei welchen Verkehren oder verfahren eine Bearbeitung Aussicht auf erfolg versprechen würde[/FONT][FONT="]’.[/FONT]
[FONT="]
[/FONT]
[FONT="]Speculation on the ‘Amerikanische schlüsselfernschreibverkehre’[/FONT]
[FONT="]Unfortunately the US cipher teleprinter cannot be identified from the German reports. However the list of possible US cipher machines is short. In 1944 the US Armed Forces used the teleprinters Sigtot and Sigcum plus there is a small chance of the Sigaba being used to send this traffic even though it was not a teleprinter.[/FONT]
[FONT="]1). SIGABA: The Converter M-134-C/ECM MARK II was an offline cipher machine but the report ‘Achievements of the Signal Security Agency in World War II’, p42 says that it had an ‘auto’ function which printed the ciphertext in a teleprinter tape which could then be sent via a teleprinter unit for rapid transmission. [/FONT]
[FONT="]2). SIGTOT: The sigtot teleprinter was a one time tape system, meaning that each transmission used a tape of randomly generated output in order to ensure that no one could decrypt the contents of the message. If the same tape was used twice then it would be possible to solve that particular message but not additional ones. [/FONT]
3). SIGCUM/SIGHUAD: The Converter M-228 SIGCUM and its modification SIGHUAD were used in large numbers in the period 1943-45. The report ‘important contributions to communications security, 1939-1945; summary of contributions made by mr. Friedman’, p6 says:
[FONT="]‘By 5 June 1944 a total of 3.200 of these machines had been built and 1.488 issued for use, including 200 to the Navy. The machine was employed to encipher a tremendous volume of traffic, including raw material for cryptanalysis from all intercept stations. Under the special conditions and with some modification (Sighuad) the machine was also used in special circuits in Washington, between Arlington Hall Station, the Military Intelligence Service in The Pentagon, of the highest classification. This same modification (Sighuad) permitted the machine to be used by the Air Forces in the U. S. and in the Pacific, to transmit, by radio meteorological and weather data, thus greatly facilitating operations’.[/FONT]
[FONT="]At this time we can only speculate but it seems reasonable to assume that the system the Germans called ‘Amerikanische schlüsselfernschreibverkehre’ was probably the Converter M-228. [/FONT]
The expert on cipher teleprinters at Inspectorate 7/VI was the mathematician Heinrich Döring. It is again reasonable to assume that he was one of the people who examined and solved this traffic.
http://chris-intel-corner.blogspot.hu/2016/01/compromise-of-us-cipher-teleprinter-in.html